The Internet of Things (IoT) is doubling its current 23 billion connected devices to 75 billion by 2025. Cybersecurity is already failing to catch up to the current pace of IoT development and innovation, so introducing more devices into enterprise ecosystems seems precarious.
Without a strong strategy for deploying new IoT systems with robust security protocols, enterprise IoT ultimately stands to lose billions of dollars from security attacks. But while the future appears dark, is there actually a silver lining to this all?
The Importance of Strong IoT Cybersecurity
IoT ecosystems don’t just include employee mobile phones; they also involve sensors, cloud setups, analytics, maintenance software, and much more.
Hacking a single part of such a complex system can result in the takedown of a whole operation for an unpredictable amount of time. And on the other hand, attacking many of an enterprise’s devices at once (known as a distributed denial of service attack) can also immediately halt entire ecosystems.
For example, in the Mirai botnet attack, the virus scanned the Internet for specific IP addresses of known IoT devices. Using telnet, a standard software on many machines running Linux, the virus attempted 60 common username-password combinations.
If it worked, the virus installed malware on the IoT device, turning it into a compromised device working like normal on the front end. But when the Mirai attack was initiated, it combined the forces of multiple compromised IoT devices to take down startup websites and services across the world. Unsurprisingly, this created a noticeable global stir among consumers, developers, and enterprises alike.
According to recent studies, 10% of consumer devices get hacked annually in the U.S. IoT devices are monitored even less than consumer devices. On top of this, the devices are expensive, so most enterprises are using outdated iterations. These are the exact type of conditions that make for an ideal hack.
Proactive Measures Against Hacks
Industrial IoT is ripe for malicious hacking, according to Eddie Habibi, the CEO of industrial cybersecurity firm PAS Global. Habibi says that most industrial IoT users won’t update their decades-old devices for a few more decades, which is a very scary sentiment.
Last year, a casino’s internal network was hacked through one of their internet-enabled aquarium thermometers. After breaching the network, the attackers found and downloaded a database of high-paying customers to the cloud.
This example illustrates that absolutely any unsecured device in an IoT ecosystem can bring down a business and leave lasting consequences for its customers as well.
All enterprises must get a clear picture of their security vulnerabilities before investing in new devices or upgrading security protocols. Most businesses should do a discovery of devices and then monitor, isolate, and segment them.
Additionally, some free-of-cost measures include requiring all devices to change passwords to be stronger and always unique as well as reviewing and adjusting your system privileges. Better device management, information security, and threat protection are also proactive steps your business can take.
Enforcing and Regulating Enterprise Security
There aren’t standardized security guidelines for enterprises. Some online organizations (and recently, governments like the UK’s) have published frameworks and minimum requirements, but there is no official system in place to enforce and regulate security across every industry.
This set of guidelines will take decades to finalize globally, and we don’t have that time nor do we have enough willing parties. It cannot be a one-time policy publication; it must evolve and grow with IoT’s strengths and weaknesses.
Additionally, IoT cybersecurity continuously gets placed last on the list of priorities for developers working on a minimum viable product. Cybersecurity isn’t like other typical product features; great cybersecurity works invisibly in the background, but poor security reveals itself with due time.
Looking at the Bright Side
Fortunately, there might be simpler enterprise IoT security solutions in the works.
For example, Seattle-headquartered tech giant Microsoft launched Azure Sphere recently; it includes an operating system and a cloud security device to bring intelligence, security, and functionality to microcontroller-based devices, which make up billions of the IoT devices in use today. Azure Sphere promises to protect IoT data endpoints, data pipelines, and custom-built cloud applications in a given IoT environment.
Besides this, the troubling lack of security for IoT is making friends of enemies.
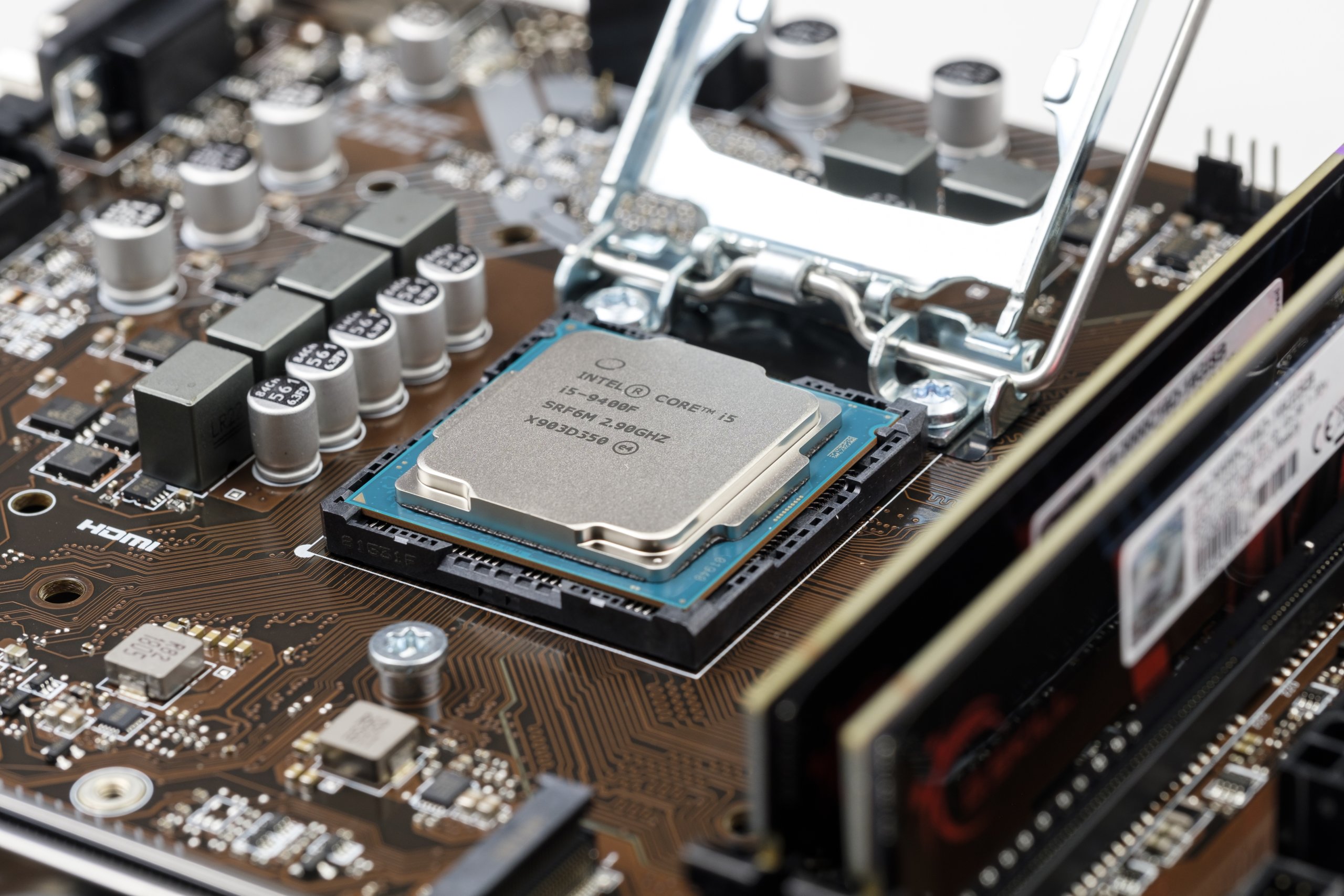
Intel and Arm also recently teamed up in a rare collaboration; the two usually compete in the microchip and hardware space. The companies want to give enterprises a better way to add sensors and devices securely to their IoT ecosystem. Both companies will embed data on each new device they power, hoping to create a more secure path to cloud connectivity.
Michela Menting is the managing director at ABI Research. Menting says, “Intel and Arm are simplifying one of IoT’s most complex and challenging barriers with regard to streamlining the manufacturing and security deployment workflows for IoT.”
She continues, “This is an ROI win for the customer, who will be able to deploy both Intel and Arm based devices at a lower cost and with less friction between IT and OT [operational technology] while at the same time retaining flexibility over their data and cloud partner choice until the deployment phase.”
Working Toward a Safer Future
Microsoft, Intel, and Arm are far from the only tech innovators looking to give IoT security a much-needed boost. Hopefully, some of the solutions currently in development end up being the safety net that we so desperately need for IoT to expand into society safely.
And hopefully, we don’t wait until another IoT cyberattack has time to convince us to take security seriously.
What are your thoughts on the current state of IoT security for enterprises and consumers? Do you feel safe utilizing the technology? Let us know what you think in the comments below!