 China’s garnered plenty of media attention lately, mostly in relation to the controversy surrounding Google’s censored search engine for the country. But now, there’s a new unsettling story to steal the spotlight.
China’s garnered plenty of media attention lately, mostly in relation to the controversy surrounding Google’s censored search engine for the country. But now, there’s a new unsettling story to steal the spotlight.
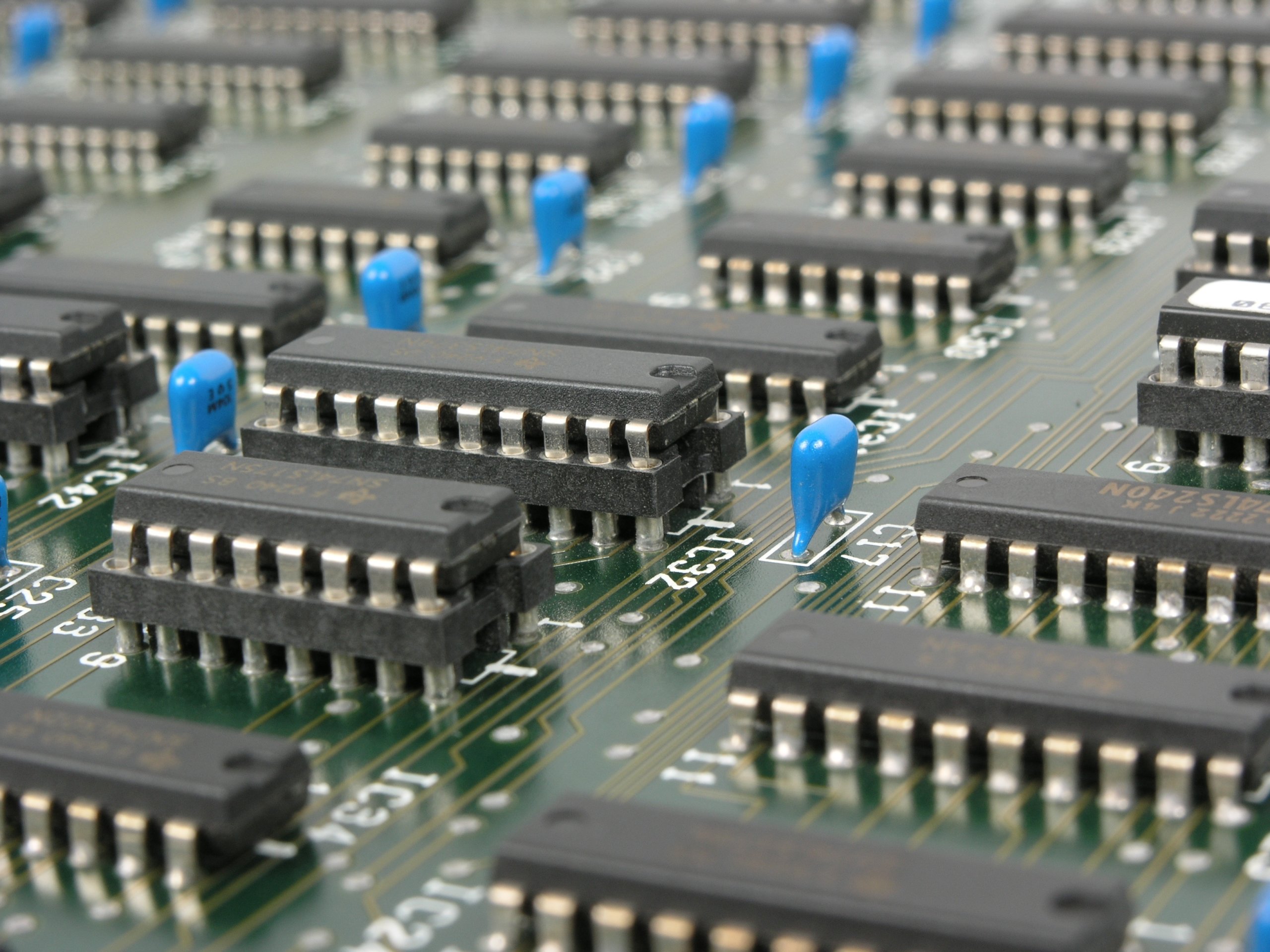
It was recently discovered that motherboards shipped from China for use by Apple and Amazon had a tiny microchip on them. This hack hit almost 30 U.S. companies in total, leaving a chasm in cybersecurity protocols for the nation’s technology supply chain.
It All Began in 2014
Supermicro is an American technology company that sells motherboards and servers to other large tech organizations. The company’s customers were the ones hit by the Chinese microchip hack; in 2014, the U.S. government received extremely specific intelligence: China was planning to insert malicious microchips into Supermicro motherboards shipped in U.S. products.
The investigation only began in mid-2015 when the U.S. government got more concrete evidence. Apple and Seattle-headquartered Amazon turned over motherboards with suspicious chips on them to the FBI.
Since it’s been three years of investigation, we do have some information now. For example, investigators believe that the microchips let hackers create an entrance into any network that the malicious microchip has connected to. The investigation also found that, most likely, the chips were inserted at factories in China, rather than in transit to America.
Because hardware hacks are traceable by any number of records used throughout the supply chain, this is an especially troubling attempt by China to hack into American networks. But if a hardware hack can make it past scrupulous inspectors, it has the potential to create more devastating, long-term consequences.
An Unprecedented Move
One big indication that this was a planned hack is that China, in particular, is the only nation in the world who could possibly carry out this large of an infiltration. The country manufactures 75% of all mobile phones and 90% of all PCs globally.
Joe Grand is a hardware hacker. He says, “Having a well-done, nation-state-level hardware implant surface would be like witnessing a unicorn jumping over a rainbow. Hardware is just so far off the radar, it’s almost treated like black magic.”
Although the chances of pulling off a hardware hack are low, as Joe said, when it’s pulled off, it’s like voodoo. According to U.S. government officials, this marks the “most significant supply chain attack known to have been carried out against American companies.”
Just Say No
In the time leading up to this writing, Amazon, Apple, and Supermicro all deny reports of the malicious chips’ origins, history, and involvement. Amazon disputed, “It’s untrue that AWS knew about a supply chain compromise, an issue with malicious chips, or hardware modifications when acquiring Elemental.”
Apple’s statement said, “On this we can be very clear: Apple has never found malicious chips, ‘hardware manipulations’ or vulnerabilities purposely planted in any server.”
And Supermicro wrote, “We remain unaware of any such investigation.”
The Chinese government also refuted all claims of adding malicious hardware to outgoing technological goods. The government issued a statement and expressed the sentiment that they’re on the same side as the U.S., saying, “Supply chain safety in cyberspace is an issue of common concern, and China is also a victim.”
The Full Extent Is Unknown
There are plenty of rumors and misinformation flying around. No one really knows the full extent of the microchip infiltration; after all, if this has been going on since 2014, how many of our devices are outfitted with a malicious microchip that could hack into our network at any moment?
The U.S. government speculates other scenarios. One official says China wants long-term access to sensitive corporate and government data and networks. However, according to Bloomberg Businessweek, “no consumer data is known to have been stolen.”
According to U.S. officials, the hack happened in this sequence:
- The Chinese government commissioned a military unit to engineer a tiny microchip, no larger than the tip of a sharp pencil. Some chips look like signal conditioning couplers. The chip was to have features like memory, networking abilities, and processing power in case of an attack.
- Supermicro’s manufacturing lines in China inserted the microchips into motherboards.
- The motherboards were used in servers sold by Supermicro.
- Apple, Amazon, and more than 20 other companies bought these servers and distributed them across the globe for use.
- When the motherboard is activated, the microchip changes a setting on the computer’s operating system to allow modifications. The chip can also communicate with other compromised computers.
Pulling the Root of the Problem
Supermicro’s stock recently stopped trading on the U.S. stock market. It happened a few weeks before the news broke about the multi-year-long history surrounding their compromised motherboards. But the company is a major player in the billion-dollar market for customized motherboards; web hosts, banks, and cloud computing platforms all over the world use Supermicro’s hardware.
The U.S. government is still investigating if spies have infiltrated Supermicro or other American companies. As one U.S. official puts it, “Think of Supermicro as the Microsoft of the hardware world. Attacking Supermicro motherboards is like attacking Windows. It’s like attacking the whole world.” Indeed, millions of motherboards are compromised virtually all over the world, with millions more getting shipped to the U.S. every year.
Following Businessweek‘s story, the Chinese government released an official statement, saying, in part, “China is a resolute defender of cybersecurity. … We hope parties make less gratuitous accusations and suspicions but conduct more constructive talk and collaboration so that we can work together in building a peaceful, safe, open, cooperative and orderly cyberspace.”
This entire situation is troubling, and it’s hard to know who’s telling the truth. Immense amounts of damage could be caused by something as small as a pencil tip. Why was the public only notified now if this has been going on for years? Could tech companies be harboring spies?
Unfortunately, it’s safe to assume that we’ll probably always have more questions than answers about this conundrum. And it also shines a light on the potential severe consequences extending to all of society, not just software engineers, mobile app developers, or other tech industry patrons.
What do you think should be done about all of this? Let us know in the comments.