The Internet of Things (IoT) is ushering in a new era in which man and machine will be more connected than ever before. People are increasingly investing in IoT technology of many shapes and sizes: connected lightbulbs, smart assistants, speakers, and even toilets are all now IoT-enabled.
But unless IoT security gets better, this revolution will come at a steep price — these affordable interconnected devices create potential for disastrous security problems that can affect individuals, businesses, and society as a whole.
Everyone Wants In on IoT
It’s not only consumers that are buying into the idea of IoT. Companies have also been expanding their inventory to include more sensors, remote monitors, and other gadgets that help them streamline operational processes and become more profitable.
And governments are getting in on the action as well. Metropolitan areas across the world are racing to reinvent themselves as smart cities to capitalize on promises of better energy efficiency, reduced traffic congestion, and improved resource management.
As a result, the number of IoT devices is beginning to reach into the tens of billions and should hit the 20-billion mark by 2023. The interconnected world they’re creating is undoubtedly bringing benefits of all sorts to their users. But because many of these devices don’t have proper security protection, it’s also making the risks higher.
Whose Responsibility Is It?
There’s been an ongoing debate about who should take responsibility for IoT security: device makers or governments? But part of the problem is definitely caused by IoT developers and manufacturers. Many of them are small, unknown, and thus don’t have brands or reputations to protect. On top of this, it would seem that all that matters to them is their bottom line; their main objective is to produce as many devices as possible to sell as cheaply as possible.
With all of this being said, it’s no surprise that cybersecurity doesn’t register as a real concern for these device makers. In a survey of 950 companies that both create and use IoT tech, security company Gemalto discovered that 48% of companies employing IoT in the workplace don’t have any mechanisms in place to detect hacks. But nearly all respondents did think that security was integral to winning customers over.
Still, the survey revealed other data points that show these companies aren’t putting their money where their mouth is —security only accounts for 15% of the budget for IoT companies on average. This is up from 13% in 2017 but is still a laughable (and sad amount). Especially when you consider that data breaches now make headlines nearly every month.
Strangely, these figures did match another finding: only 14% of respondents believe that providing security was an ethical responsibility. That number has actually grown by more than three times what it was in Gemalto’s 2017 survey. So it possibly hints that businesses may be thinking more seriously about security.
As far as that goes, consumers definitely are — 62% believe that security needs to become better. The survey did not determine specifics about whether respondents were planning on improving their IoT security endeavors. But it did hint they think governments should step in to make it right: 79% of respondents are looking to governments to set and enforce higher security standards.
The Consequences of Crummy IoT Security
IoT devices are useful for a variety of applications. But this means they also have a wide range of security vulnerabilities like unencrypted communication, insecure web interfaces, and weak passwords. So with thousands of identical and insecure devices now scattered throughout the world, IoT now has a big bullseye that’s too big for hackers to ignore.
And many manufacturers make it pretty easy to hit that target. Believe it or not, lots of IoT device makers set an unchangeable administrative password for a particular device model — meaning the same password works for thousands of devices. This, unfortunately, happens more often than any IoT user would hope and is something that recent government legislation is trying to fix.
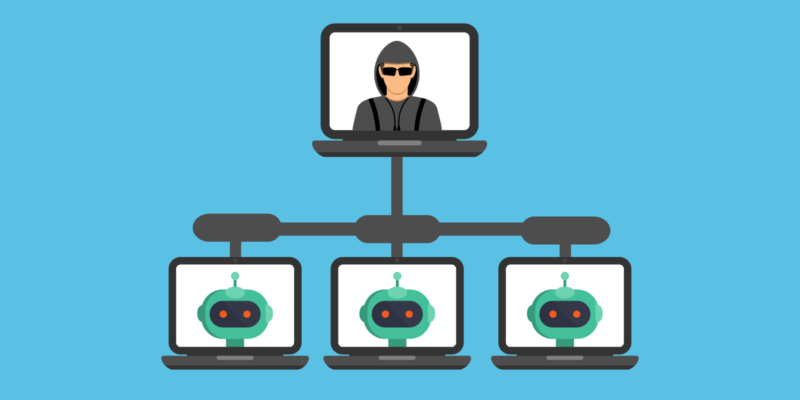
Hackers can simply run a program that searches the internet for these devices, log into them, take control, and install malicious software to recruit the device into their botnet army (a vast network of computers). Once done, the devices function normally until the hacker wants to do something. From there, the hacker can issue instructions to carry out anything that a computer can do, such as clog up data connections with a flood of internet traffic (this is known as a distributed denial-of-service attack).
Traditionally, botnets were comprised of laptop and desktop computers. But the unprecedented growth of unsecured industrial sensors, webcams, and other connected devices carry far more has resulted in the potential for much for destructive capabilities.
With thousands of botnets at their beckoning, hackers can carry out DDoS attacks that shut down company and government servers or block whole regions of the internet from being accessible. In 2016, you may remember such an incident happening that resulted in huge sections of the U.S. east coast not being able to access Amazon, Netflix, and PayPal.
This particular attack, known as Mirai, wasn’t the result of some elite hacker organization from San Francisco, Beijing, or some other tech hub. It was caused by three teenagers who wanted to suer more than 100,000 hijacked devices to gain an upper hand in the “Minecraft” video game.
Imagine what could have happened if a more nefarious entity was behind such a catastrophic attack. The same networks that IoT devices and other gadgets use to simplify our lives are linked to physical security systems, help manage traffic lights, and allow self-driving cars to talk to each other. So the consequences could be severe.
On that note, we’ll end this article with a simple reminder: Check your IoT devices, folks. Until someone takes proper responsibility for this lack of security, the onus falls on each of us to protect ourselves.