
The Complete Guide to Healthcare Mobile App Development
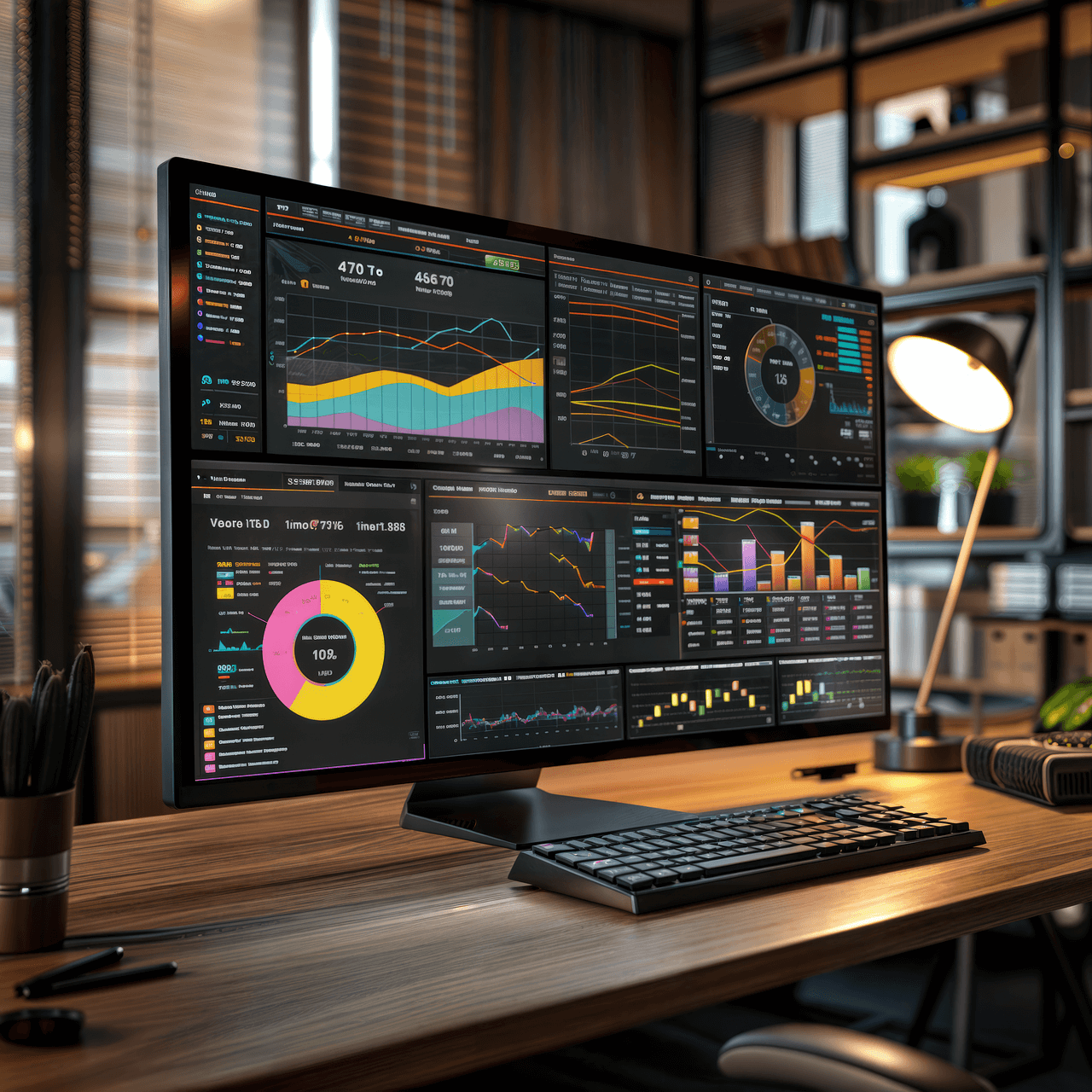
Healthcare mobile app development has evolved from basic appointment scheduling
Read about the latest in mobile and internet technology.
Articles and tips focused on tech startups.

Healthcare mobile app development has evolved from basic appointment scheduling

After reading this article, you’ll: If you’ve ever launched a

After reading this article, you’ll: The energy and utilities sector

After reading this article, you’ll: The Trust Crisis Reshaping the

After reading this article, you’ll: The proliferation of mobile devices

After reading this article, you’ll: Every mobile app developer knows
Key Takeaways In the competitive landscape of mobile app startups,

Key Takeaways The Global App Economy Has a Dirty Little
Key Takeaways The Delete Button Paradox: Why Letting Users Leave

Key Takeaways The High-Stakes Game of Mobile App Permissions Picture

Original Article Featured in Entrepreneur.com. When my company began, we were

Original Article Featured in Forbes. The 5G era is upon us.

This guest-post is courtesy of our partners at Gummicube. While


Original article written by Dave Kerpen for Inc. Magazine There

Analytics firm Localytics recently released some numbers that chilled mobile

Eight hours a day. Five days and 40 hours per

When the founders of AirBnB pitched their idea to Paul

Mobile tech revolutionized transportation, finances, and communication. In the short

Twenty years have passed since eBay democratized auctions and seven